Key Assumptions When Setting Up Quik!
Please Read!
It is important to be aware of what assumptions are included in the Quik! system design. The following assumptions are included in the design of this system:
Setup
- The customer will implement Quik! within their application (i.e. Quik! is not necessarily hosting an application nor building one on behalf of enterprise customers).
- The customer must have a valid Master Customer Account with Quik! and supply Master Credentials with each request (end-user credentials that are not the Master Credentials will not work).
- If the Quik! Forms Engine component is installed on your computer it may need read/write access to your computer or server's temporary file location or a location specified by you.
- The customer will implement one or more web services with a Quik! server in order to retrieve/send data used with the Quik! services and APIs.
- As of April 2020, supported browsers include: Internet Explorer 9.0+, Safari 5.1+, Firefox 12+, Opera 12+, Chrome 19+. Browsers must have Javascript enabled
- To use e-signature:
- E-signing requires SSL (HTTPS) and without it will result in "Access Denied" in Internet Explorer browsers.
- Customer will directly procure and use their own account with the signing vendor (i.e. DocuSign, Signix), set up a vendor-specific API Key and reference Efficient Technology Inc as the referral source.
- Customer assumes responsibility for the validity and acceptance of electronic signatures with the form owners, if electronic signature is used.
- Customer may need to deploy the QuikESignTransport in the same domain as the HTML forms in order to facilitate the e-signing process.
- Customer will be responsible for calling the e-sign vendor's APIs to retrieve the current signing status and to download final signed documents (i.e. Quik! is only designed to send documents to e-sign vendors to kick off the e-signing process)
Security
- Quik! servers do not store, save or persist any client data that may be transmitted to the server for the purposes of generating, printing, signing or transmitting forms. Data, if sent, is encrypted during transport and discarded the moment it has been processed.
- The customer's computer, server or program is responsible for deleting any temporary files that are generated by the use of the software (e.g. HTML files, error logs, etc.).
- The customer will create a secured SSL connection between their user's browser and their web application for delivering Quik! output and forms to their user.
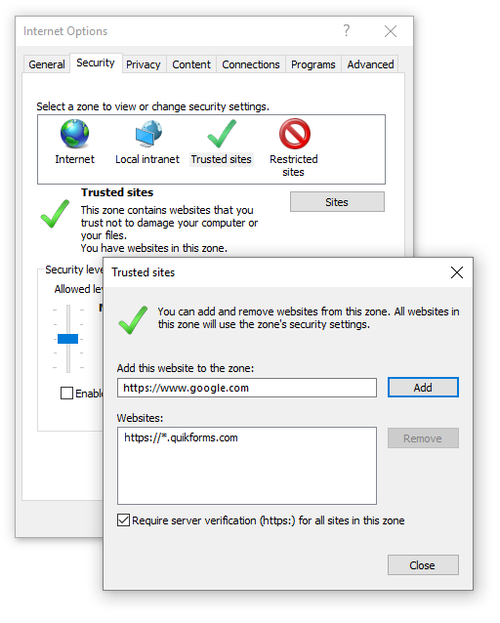
- Internet Explorer may restrict certain features (e.g. print, save, etc.) due to security settings. To prevent this, be sure to:
- Host the Quik! Form from an HTTPS location. (HTTP non-secure is allowed, but not recommended)
- Add our domain (quikforms.com) as a Trusted Site in Internet Options → Security → Trusted Sites → Sites
Limitations
- Requests to combine multiple forms into a single form package are limited based on file size, page count and form count. Although you may get successful response from Quik! for large package requests, please refrain from requesting more than 20 forms in a single package or more than 100 pages at a time. Quik! limits form requests to 100 FormIDs, but that doesn't mean 100 will work due to the resulting file size.
- The HTML form viewer automatically expires and pages are no longer viewable after a maximum of 10 days from the date they are generated, or earlier at the customer's discretion.
- Forms will not fully function for iPad users using Private Browsing (e.g. the SAVE and LOAD buttons will not allow for local storage and saving as designed by Apple).
- Editable PDFs cannot be saved unless the user has a version of Adobe Acrobat that enables saving. Also, field collisions with combined forms may occur in editable PDFs due to standard PDF functionality and design.
Domains to Whitelist
When integrating with Quik!, you will need to ensure connections with our various domains are clear and unobstructed. We recommend the following IP Addresses, domains, and sub-domains to be whitelisted or made exempt from your security policies:
- www.quikforms.com
- quikforms.com
- websvcs.quikforms.com
- qcc.quikforms.com
- quikformsmanager.com
- etiforms.com
- Production IP Addresses - the following IP address may be in use (or resolved by DNS) when communicating with Quik! APIs.
- 54.163.253.215 - QuikForms.com IP
- 184.73.172.182 - QuikForms.com IP
- 34.194.148.75 - QuikForms.com IP
- 34.192.179.113 - Network Gateway IP
- 34.193.98.155 - Network Gateway IP
- Disaster Recovery IP Addresses
18.220.1.124 (inbound)
3.134.188.250 (inbound)
3.134.182.3 (outbound)
3.134.56.161 (outbound)
For help regarding Quik! Forms and the Quik! API
Email: support@quikforms.com | Phone: (877) 456-QUIK